Zero Trust Architecture Implementation in SMBs: A Bayesian Risk Analysis Model and Empirical Validation
Why the "Small" in SMB is a Cybersecurity Target‑And How Zero Trust Levels the Playing Field
The 1,500‑Employee "Small" Business
Small‑to‑Medium Businesses (SMBs) are the undisputed economic backbone of the global workforce, representing nearly every enterprise in the United Kingdom, Australia, and the United States. But in the eyes of a Cybersecurity Strategy Consultant, the "Small" in SMB is a misnomer that invites complacency. Per the US Small Business Administration (SBA) guidelines, an SMB can employ up to 1,500 people.
These are not just "mom and pop" shops; they are significant enterprises that handle massive amounts of regulated data. For a firm of this size, a multimillion‑dollar fine from GDPR or HIPAA isn't just a line item‑it's a terminal event. In this landscape, Zero Trust Architecture (ZTA) has shifted from a luxury for the Fortune 500 to a survival necessity for the mid‑market.
The 20% Mitigation Miracle: Science, Not Superstition
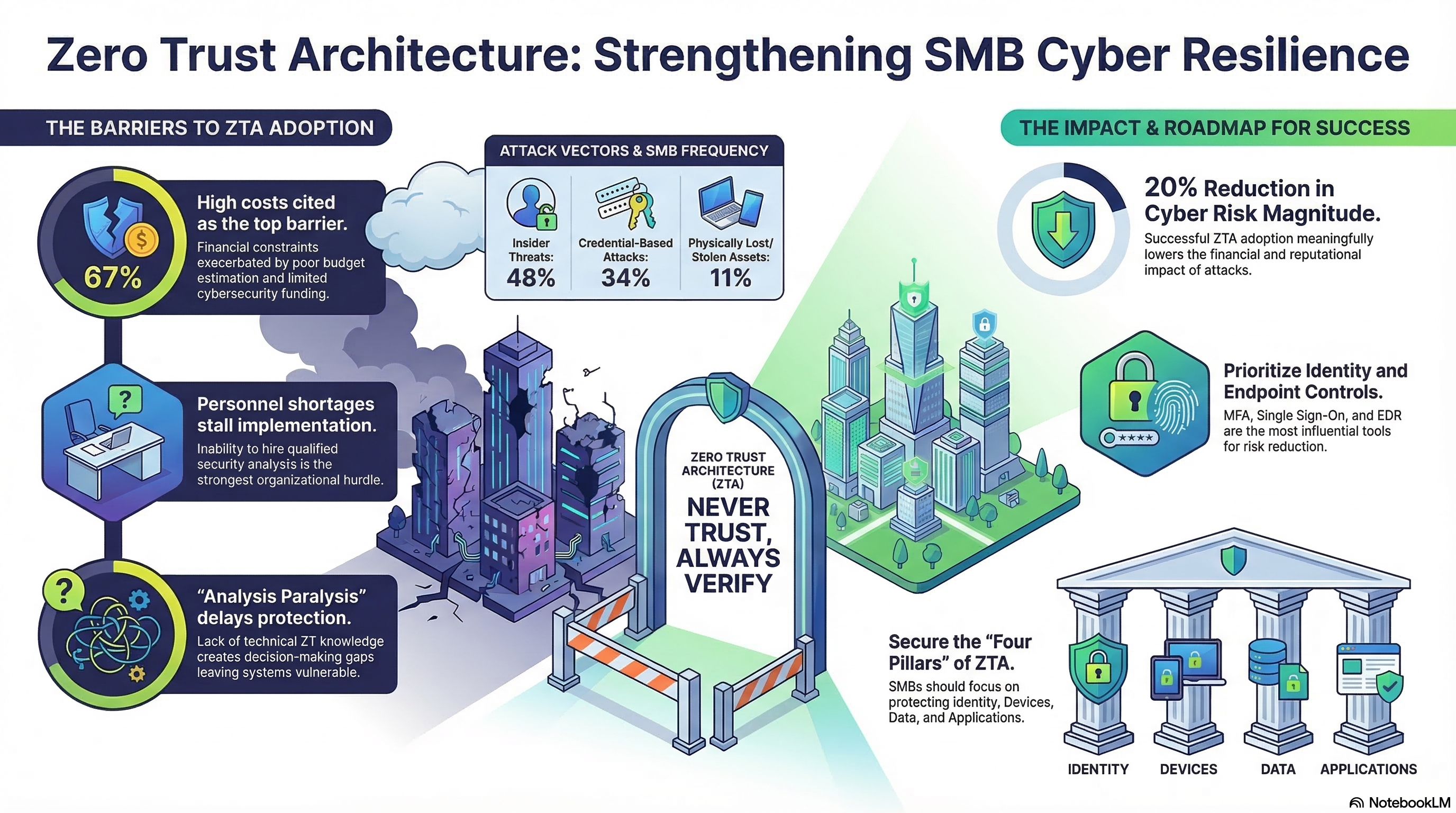
For years, Zero Trust was more of a marketing buzzword than a measurable strategy. However, recent research using Bayesian Network models has finally quantified the "miracle." By running 20,000 Monte Carlo simulation iterations, researchers proved that ZTA can reduce the magnitude of cyber risk by up to 20%.
For an SMB operating on tight margins, a 20% reduction in risk magnitude is the difference between operational continuity and bankruptcy. As the study's abstract notes:
"ZTA could meaningfully reduce the risk magnitude by up to 20 percent and the likelihood of data breach resulting from certain attack scenarios."
By moving away from "implicit trust" models, businesses aren't just buying a tool; they are mathematically lowering the probability of a catastrophic failure.
The Phishing Red Herring: Your Biggest Threat is Already Inside
If you read the headlines, you'd think phishing is the only way hackers get in. While phishing is a common entry point, the data on actual historical losses for US‑based SMBs tells a much more localized story. According to the Advisen dataset of US cyber incidents:
- Insider Threats: 47.92%
- Credential‑Based Attacks: 34.30%
- Phishing: 3.29%
This "Phishing Paradox" suggests that while we train employees not to click links, we ignore the fact that the danger is already "inside the building." Whether through malicious intent or simple negligence, internal actors and compromised credentials represent the lion's share of devastating events. ZTA levels the playing field by assuming the network is already compromised, mandating continuous authentication for every user, every time.
Breaking the 51% Analysis Paralysis
The greatest barrier to security isn't a lack of software‑it's the "Talent Trap." Sensitivity analysis reveals that the inability to hire a qualified security analyst is a more significant hurdle for SMBs than a simple lack of technical knowledge.
The research shows a dangerous causal link: when a business suffers from both limited cybersecurity awareness and a gap in Zero Trust technical knowledge, the probability of "Analysis Paralysis" jumps to 51%. This organizational freeze‑up leaves firms vulnerable because they are too overwhelmed to start. For my clients, the tactical pivot here is clear: if you cannot hire internally, you must leverage Managed Security Service Providers (MSSPs). The study confirms that MSSPs are a viable workaround to bypass the hiring shortage and jumpstart implementation.
Stop Buying WAFs: DE and RBAC are the Only "Power Couple" That Matters
When budgets are tight, you have to prioritize the controls that actually move the needle. While many SMBs reflexively buy Web Application Firewalls (WAF), the sensitivity analysis of the RiskMagnitude node (Fig. 9) shows that WAFs have a comparatively weaker effect on reducing overall risk.
Instead, focus on the defensive "Power Couple":
- Data Encryption (DE)
- Role‑Based Access Control (RBAC)
These two variables are the most influential risk reducers in the entire Bayesian model. If you lock down the data itself (DE) and strictly limit who can access it (RBAC), you render an attacker's presence largely irrelevant. Even if they get in, they can't read the "prizes" they've stolen.
The Maturity Leap: From 71% Risk to Resilience
A business operating under a traditional "implicit trust" model faces a 71% posterior probability of a data breach. Many owners find this number so high they simply give up, but the "Maturity Leap" shows that progress‑not perfection‑is the goal.
The simulation of implementation scenarios reveals a clear path:
- Base‑Case (No ZT): 71% breach risk.
- Scenario 1 (Partial Implementation): Cuts risk to 56%.
- Scenario 3 (Full Pillar Maturity): Slashes risk to 40%.
The takeaway is encouraging: even a partial shift toward Zero Trust principles (Scenario 1) provides an immediate and measurable reduction in risk. You don't need to be perfect on day one to be significantly safer.
Beyond the Insurance Safety Net
Cyber insurance is a vital reactive tool, but it is not a strategy. While insurance might cover a portion of your financial loss, it cannot restore lost customer trust, fix operational disruptions, or erase the reputational stain of a breach.
Zero Trust Architecture is the proactive alternative. It prevents the operational paralysis that insurance can only compensate for after the fact. In an era where 48% of threats are internal and 1,500‑employee firms are prime targets, the question is no longer whether you can afford Zero Trust. The question is: can you afford to keep trusting a network that nearly half of your threats already call home?