A stochastic SIR model for cyber contagion: application to granular growth of firms and to insurance portfolio
The Virus in the Machine: Why Your Next Ransomware Attack Will Look Like a Biological Pandemic
Cybersecurity risk has transitioned from a back‑office IT concern into a systemic global threat comparable to climate change and geopolitical instability. Recent data from GuidePoint Security reveals the scale of this shift, with ransomware attacks experiencing explosive growth of 76.8% between 2022 and 2023. We are moving away from a “high frequency, low severity” landscape into a “contagion” world where the severity of attacks scales exponentially.
This is no longer a matter of isolated incidents; we are witnessing the rise of cyber‑contagion. Strategic leaders must recognize that modern attacks are not random events but follow the same mathematical and structural rules as biological outbreaks. Weaponizing epidemiological data is now essential for survival in an increasingly interconnected digital economy.
Your Network is an Ecosystem: The SIR Model
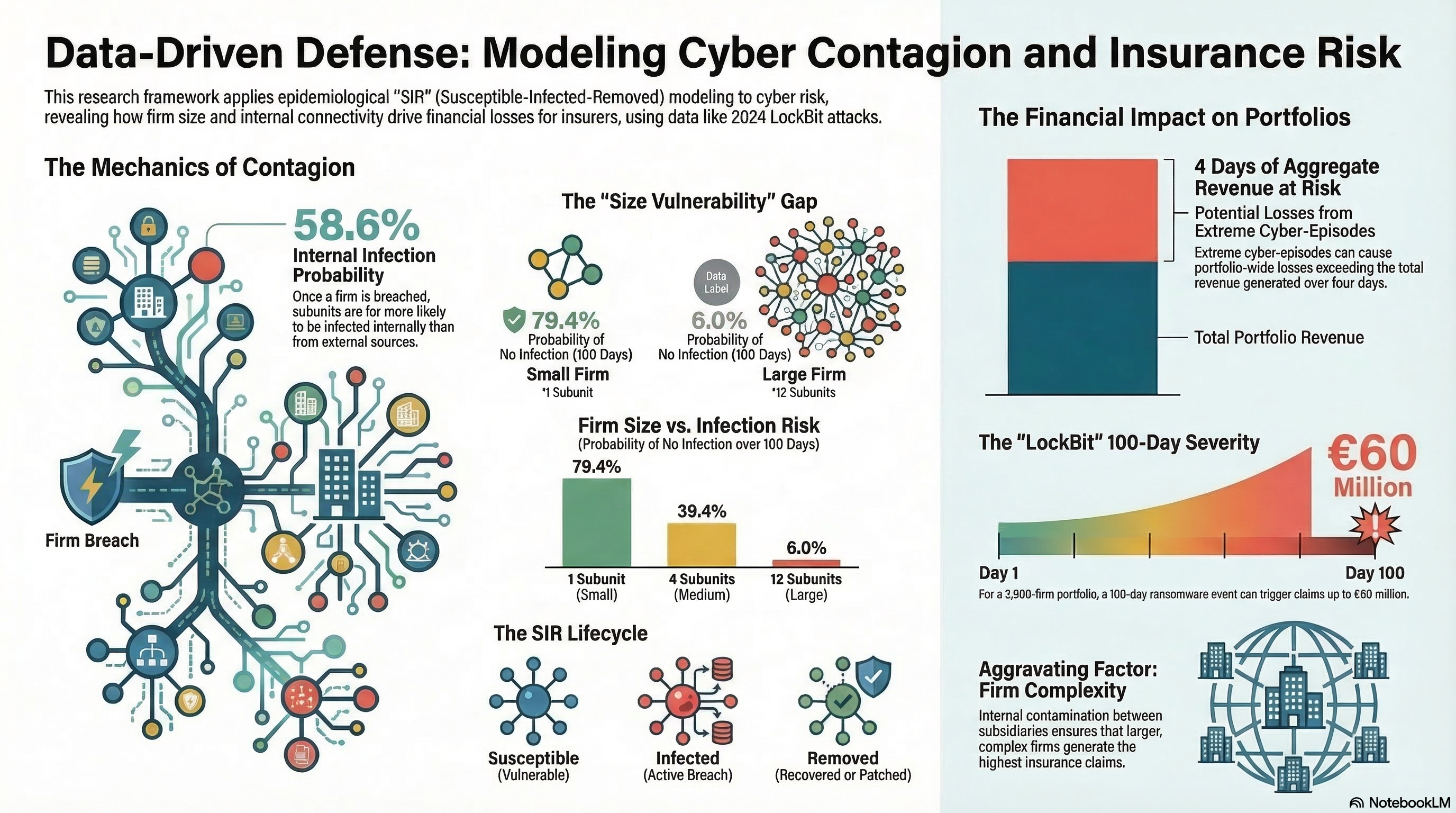
To understand how ransomware navigates a corporate landscape, we apply the “SIR” (Susceptible‑Infected‑Removed) compartmental model, a framework traditionally used to track diseases like influenza. Every organization or internal subunit exists in one of these three states during an outbreak. Susceptible units are exposed but not yet hit, Infected units are compromised and capable of transmitting the malware, and Removed units represent the recovery capacity of the IT team where systems are secured or patched.
As the research highlights:
“Cyber‑attacks share key mechanisms with biological epidemics, including the presence of a susceptible population, infection and recovery dynamics, peak intensity, prevalence, and network or cluster structures.”
By adopting this biological analogy, insurers can move toward dynamic risk pricing rather than static annual assessments. This model allows risk managers to calculate the “force of infection,” predicting how quickly a virus will jump through shared networks and supply chains.
The “Size Trap” and the Day 0 Vulnerability
Research utilizing Zipf's Law‑the observation that a few large entities account for the majority of a system's mass‑reveals a counter‑intuitive "Size Trap.” Firm size is the primary driver of vulnerability, with mid‑to‑large‑size organizations acting as the “canaries in the coal mine.” Larger organizations are not simply bigger targets; they are hit significantly earlier in the lifecycle of a cyber‑epidemic.
The data is striking: for a regional epidemic, firms of the largest size category reach their “New Susceptibles” peak at Day 0. In contrast, the smallest firms do not reach this same peak until Day 41. For the C‑suite of a major corporation, this means your risk exposure begins the moment an outbreak is detected anywhere in the market.
The Binary Risk of Internal Contagion
While organizations often obsess over the "External Contagion" from hackers, the true “silent killer” is "Internal Contagion" within the corporate perimeter. The probability of an infection originating from the outside world on any given day is remarkably low, peaking at approximately 0.45%. However, once the perimeter is breached, the risk becomes a "Binary Flip.”
The probability of an “in‑firm” infection from an already compromised sister subunit is over 58%. This secondary infection is the primary driver of systemic solvency risks, as seen in the LockBit ransomware episode between May and July 2024. Despite the disruption of the LockBit group by Operation Cronos, the interconnected nature of modern Granular Growth Models means that lateral movement remains the greatest threat to organizational integrity.
The 100‑Day Financial Stress Test
When a cyber‑contagion event takes hold, the financial storm is both swift and severe. Simulations of a typical 100‑day cyber‑episode show that an insurer might need to compensate a portfolio for losses equivalent to two full days of aggregate revenue. While this aggregate figure sounds manageable, it masks the catastrophic “peak” shocks felt by individual firms.
Reality Check: During a single contagion scenario, an individual firm can see claims reach up to 75% of its daily revenue. These moments occur when internal contagion is at its height and recovery teams are overwhelmed by the volume of infected subunits requiring simultaneous remediation. This distinction is vital for understanding the difference between portfolio‑wide performance and firm‑specific catastrophe.
Conclusion: Toward Digital Immunity
The future of risk management lies in evolving from reactive patching to sophisticated Cyber Catastrophe Modeling. By using metrics like Aggregate Exceedance Probability (AEP), insurers can now conduct a “Cyber 1‑in‑100 year event” stress test to quantify systemic risks. This shift allows for more resilient capital allocation and the development of digital “herd immunity.”
We are entering an era where organizations must be modeled as biological entities to be properly protected. Current cybersecurity strategies must be re‑evaluated to determine if they are merely providing temporary relief or building true organizational immunity.
If your organization is modeled as a biological entity, is your current cybersecurity acting as a temporary patch, or a true immunity?